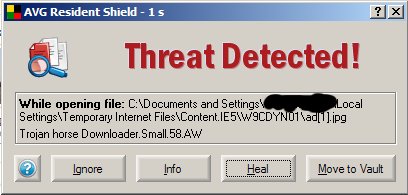
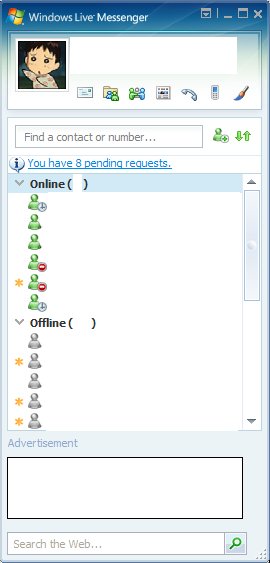
I have just launched my Windows Live Messenger (yeah, finally upgraded...) and this pops up.
Followed by this...
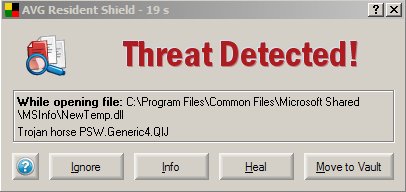
So basically ad[1].jpg is a trojan which downloads whatever NewTemp.dll is... (along with a NewTemp.bak which I have manually removed)
So newer is not always better (>.<)
Anyway, tired of how weird things keep dropping in the Temporary Internet Files folder and executing themselves, I've decided to beef up my Internet Security. Now any scripts must seek my permission to run...

So, after relaunching Windows Live Messenger...
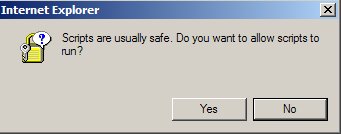
If you click yes,
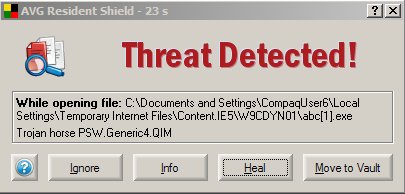
Safe. Yeah right.
Clicking no and the banner ads are gone. And no weird viruses.
However, I'm still not satisfied. I'm not sure where the trojan gets downloaded from in the first place. A query of "Newtemp.dll" on Google comes up with nothing. Nada. 0 results. So I guess it's a new variant. Doing more research, I found that a Javascript file and an HTML file was downloaded along with the "JPG" file. The HTML file is somehow linked to a page from China (with the filename woyao.htm), which when I visited (script execution still disabled of course), showed that the "ad.jpg" file is set as the cursor for the page. There is also the same script attached to it.
More research, and I've learnt that the "cursor" uses an ANI (animated cursor) vulnerability to attain remote execution priviliges. In English, that means that the bad buy can easily control your computer from wherever he is with the supposedly harmless cursor. So better patch that up.
Well, after patching, the "cursor" file is still downloaded, but the attackers can't do anything. So that's good for the time being.
Postscript: Yes, it's been confirmed. It came from the weird icons on the tabs. I've managed to patch the tabs with Tabserve to remove all of them (completely this time, not just hiding them). Now there aren't even any prompts for my permission to run scripts! How the tabs attached itself to my messenger in the first place... I don't know... yay! I can finally sleep in peace! And General Wang will be so pleased with me... (>.<)
Postpostscript: It's a trojan. A new variant. Still related to the Chinese Instant Messenger QQ. http://www.sophos.com/security/analyses/trojqqpassaou.html
Postpostpostscript: Not my computer's fault. It's the network that's flooded with the worm. My computer is fully protected and safe. Even iFrames are disabled for the time being (>.<)